 
Perfect Security Icons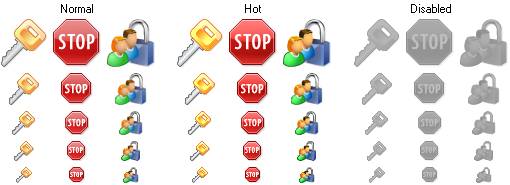
Perfect Security Icons is a collection of wonderfully-crafted stock icons for use in commercial and personal products, including software applications, websites and presentations. The icons have a bright color palette, smooth and well-rounded edges. Google translation Perfect Security Icons ist eine Sammlung von wunderbar gestaltete hat Icons für kommerzielle und persönliche Produkte, inbegriffen Software Applikationen, Webseiten und Präsentationen. Die Icons verfügen über eine breite Farbpalette, glatten und gut abgerundeten Ecken. Symbolbilder:Key, Key copy, Car key, Access key, Keys, Add key, Add key v2, Remove key, Remove key v2, Key status, No key, Lock, Unlock, Open lock, Registration, Investigation, Secrecy, Encrypt, Decrypt, Safe, Empty safe, Open safe, Broken safe, Personal smartcard, Credit cards, Shield, Protection, Virus, Folder, Documents, Hot documents, Folder sharing, Open file, Closed folder, Save, Print, Empty dustbin, Full dustbin, Burn dustbin, Trash, Add, Apply, Yes, OK, Delete, Erase, Remove, No, No USB, Cancel, Abort, Terminate, Stop, Turn off, Error, Restricted, No entry sign, Forbidden, Harmful, Disaster, Red flag, Red percent, Red star, Ignore, Warning, Virus warming, General danger, Poison, Radioactive, Radiation, Question, Question mark, Help, Info, Refresh, Sync, Clear, Clear document, Cut, Copy, Paste, Blank, Blanks, Report, Reports, Restricted page, Card, Cards, Card file, List, Mail, Attribute, Web form, Web site, Case history, Certification, Certificate, E-mail, Contact, Copyright, E-mail message, Attach, Nick, Person, User, Users, User group, Add user, Add users, Remove user, Remove users, User login, User logout, Admin, Key keeper, Black list, Police officer, Cop, Security, Locked user, Locked users, Prisoner, Spy, Thief, Death, Pirate flag, Visual communication, Ambulance car, First aid, Keyboard, My computer, Monitor, Computer, Client network, Computer access, Local security policy, Phone support, Monitor and phone, Inventory, Data transmission, PC-PDA synchronization, PC-Web synchronization, Network connection, Traffic, Computer network, VPN tunnel, Voice identification, Fax machine, Cell phones, Phone, PDA, Phones, Mobile phone, Telephone, Telephone receiver, Cable, Phone communication, Camera, Card terminal, CD, Chip, Data, Database, Database security, Filter, Pin, Archive, Pack, Unpack, Firewall, World firewall, Network firewall, Flame, Shredder, Bulldozer, Emergency on, Emergency off, Handshake, Login, Signature, ID, Office, Police, Radio transmitter, Scales, Application, Finger-print, Stethoscope, Umbrella, USB, Web camera, Location, Internet applications, Internet, Intranet, Internet access, Lock web, Earth, Web, Globe, Antivirus downloadGoogle translation Key, Schlüssel kopieren, Car-Taste, Access Key, Schlüssel, Schlüssel hinzufügen, auf Schlüssel hinzufügen v2, Ziehen Sie den Schlüssel, Ziehen Sie den Schlüssel v2, Key-Status, Kein Schlüssel, Lock, Unlock, Open-Sperre, Registrierung, Untersuchung, Geheimhaltung, Verschlüsseln, Entschlüsseln, Safe, leeren Safe, Open Safe, Broken Safe, Personal Smartcard, Kreditkarten, Schild, Schutz, Virus, Ordner, Dokumente, Hot Dokumente, Ordner teilen, Open-Datei, Ordner geschlossen, Speichern, Drucken, Mülleimer leeren, Full Mülleimer, Burn Mülleimer, Trash, hinzufügen, Übernehmen, Ja, OK, Löschen, Löschen, Entfernen, No, No USB-, Abbruch, Abbrechen, beenden, Stop, Ausschalten, Error, Restricted, keine Angabe zu unterzeichnen, Forbidden, Schädlich, Disaster, Red Flag , Red Prozent, Roter Stern, ignorieren, Warnung, Virus Erwärmung, allgemeiner Gefahr, Gift, radioaktive, Strahlung, Frage, Fragezeichen, Hilfe, Info, Refresh, Sync, Frei, Frei-Dokument, Ausschneiden, Kopieren, Einfügen, Blank, Blanks , Bericht, Berichte, Eingeschränkte Seite, Card, Cards, Card-Datei, Liste, E-Mail, Attribute, Web-Formular, Website, Anamnese, Zertifizierung, Zertifikat, E-Mail-, Kontakt-, Urheber-, E-Mail-Nachricht anhängen, Nick , Person, User, Benutzer, Benutzergruppen, Benutzer hinzufügen, Benutzer hinzufügen, Benutzer entfernen, Nutzer entfernen, Benutzer-Login, Benutzer-Abmeldung, Admin, Key Halter, Schwarze Liste, Polizei, Cop, Sicherheit, Benutzer gesperrt, gesperrte Nutzer, Prisoner , Spy, Thief, Death, Piraten-Flagge, Visuelle Kommunikation, Krankenwagen, Erste Hilfe, Tastatur, Mein Computer, Monitor, Computer, Netzwerk-Client, Computer-Zugang, lokale Sicherheitsrichtlinie, Telefon-Support, Monitor und Telefon, Inventur, Datenübertragung, PC-Synchronisation mit PDA, PC-Synchronisierung Web-, Netzwerk-Verbindung, Verkehr, Computer, Netzwerk, VPN-Tunnel, Voice-Identifikation, Faxgerät, Handys, Telefon, PDA, Handys, Handy, Telefon, Telefon-Receiver, Kabel-, Telefon-, Kamera , Card-Terminal, CD, Chip, Daten, Datenbank, Datenbank-Sicherheit, Filter, Pin, Archiv, Pack, Packen, Firewall, World Firewall, Netzwerk-Firewall, Flame, Shredder, Bulldozer, Emergency on, Not-Aus, Handshake, Login, Unterschrift , ID, Büro, Polizei, Funk-Sender, Waagen, Anwendungs-, Finger-Print, Stethoskop, Regenschirm, USB, Web-Kamera, Lage, Internet-Anwendungen, Internet, Intranet, Internet-Zugang, Web-Lock, Erde, Web, Globe, Antivirus-Download
|
Bibliothekfeatures 
Über Perfect Security IconsPerfect Security Icons is a collection of royalty-free stock icons for use in commercial and personal products, including software applications, websites, blogs, and presentations. The icons have been carefully created pixel by pixel by professional artists. They shine with a bright palette of colors, smooth and well-rounded edges. Superb in their quality, the icons will help a developer to place a truly professional feel to his project's interfaces without the need to hire a designer or spend days and even weeks on designing icons on his own. Your web products and security software will look more modern and attractive with Perfect Security Icons. Color formats include Windows XP and 8-bit formats. Available sizes are 16x16, 20x20, 24x24, 32x32, and 48x48. This icon set includes security related icons: login, guard, firewall, signature, lock, key, shield, card file and others. See your icons before placing an order. These security icons are immediately available as full-size previews on the Perfect Icons Web site. Aha-Soft plans to release the next icon collections also: Android Png Icons, iPhone Png Icons, Facebook Png Icons, Delicious Png Icons, Catalogue Png Icons, CRM Png Icons, People PNG Icons and Glyph PNG Icons. Über Perfect Security IconsGoogle translationPerfect Security Icons ist eine Sammlung von Royalty-Free Stock Icons für kommerzielle und persönliche Produkte, inbegriffen Software Applikationen, Webseiten, Blogs und Präsentationen. Die Icons sind sorgfältig Pixel für Pixel von professionellen Künstlern. Sie leuchten mit einer breiten Farbpalette, glatten und gut abgerundeten Ecken. Dank ihrer Qualität, werden die Symbole helfen, ein Entwickler, einen wirklich professionellen Look zu seinen Projekt-Benutzerschnittstellen ohne die Notwendigkeit, einen Designer anzuheuern oder verbringen Sie Tage oder sogar Wochen am Design seiner eigenen. Ihre Web-Produkte und Sicherheits-Software sieht moderner und attraktiver mit Perfect Security Icons. Color formats include Windows XP und 8-Bit-Formaten. Verfügbare Größen sind 16x16, 20x20, 24x24, 32x32 und 48x48. Dieses Icon Set enthält Sicherheit verbundene Symbole: Login, Wächter, Firewall, Signatur, Schloss, Schlüssel, Schild, Karte und andere. Sehen Sie die Bilder vor der Bestellung. Diese Security-Symbole sind ab sofort als Full-Size-Vorschau auf die Icons Perfect Website. Aha-Soft plant, die nächste Symbol Sammlungen auch die Freisetzung: Android PNG-Icons, iPhone PNG-Icons, Facebook PNG-Icons, Delicious PNG-Icons, Katalog PNG-Icons, CRM PNG-Icons, People PNG Icons und Glyph PNG Icons. |